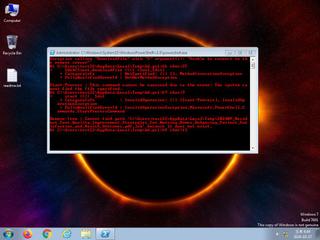
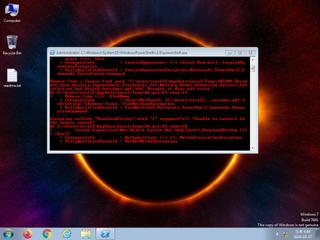
ScreenShot
| Created | 2024.10.17 16:48 | Machine | s1_win7_x6403 |
| Filename | bd.ps1 | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 10 detected (PowerShell, Boxter, Wacatac, SC205512) | ||
| md5 | 2ab24d76a4372ba60974d6661e8d0325 | ||
| sha256 | 131113c21e5fa23ab493f559ebac248302ef658da5cf62abbcea0a1e391ba8d2 | ||
| ssdeep | 96:KO1Alv0r/kmj70uYYaTZU2WuLaMYBjSRKwLxbO:KNl8o9BYX2HLaLBuo | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (15cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | Communicates with host for which no DNS query was performed |
| watch | File has been identified by 10 AntiVirus engines on VirusTotal as malicious |
| watch | Installs itself for autorun at Windows startup |
| watch | One or more non-whitelisted processes were created |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Creates a shortcut to an executable file |
| notice | Creates executable files on the filesystem |
| info | Checks amount of memory in system |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (download) |
| info | Lnk_Format_Zero | LNK Format | binaries (download) |