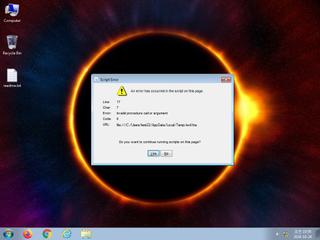
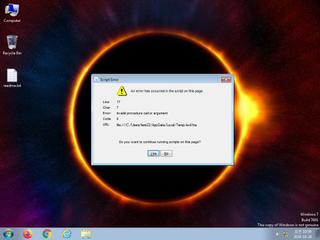
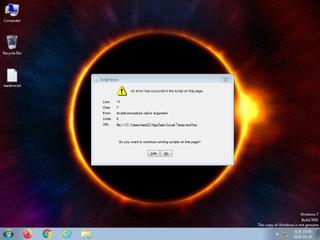
ScreenShot
| Created | 2024.10.24 11:07 | Machine | s1_win7_x6403 |
| Filename | evil.hta | ||
| Type | HTML document, ASCII text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 32 detected (CVE-2018-8174, SNIC, COBEACON, TrjGen, ebogzi, TOPIS, TyLkoyrXauN, Siggen, Inor, Veilev, Detected, NBY@7nkapq) | ||
| md5 | bbef4076e21551ff83395d537239ab87 | ||
| sha256 | c57f7ed4d9373c96cd228884c535a545c388d6edee4fae49afb7763c69450281 | ||
| ssdeep | 6144:psaVtjmheesUL+x2MreII4DMImzHvye1f:uaVtjmheesUL226JI43K | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 32 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates executable files on the filesystem |
| info | Checks amount of memory in system |
Rules (1cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | PE_Header_Zero | PE File Signature | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|