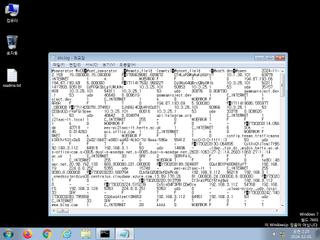
ScreenShot
| Created | 2024.12.01 02:27 | Machine | s1_win7_x6401 |
| Filename | dns.log | ||
| Type | ASCII text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 09b081750dde8d0cebad84499db9fc11 | ||
| sha256 | 1761a768518e3fca80c1386cfe13322911e8f27a3f06252f5abed6219623a00e | ||
| ssdeep | 1536:uJRlriCkA/B1rO5ZAk1Hn/U2+nZy2HWV9BsOc4XR7n6hd0P2zuIhvJW1K:urVnBV0nwnZjwdRw | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (3cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
Rules (10cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (upload) |
| notice | ScreenShot | Take ScreenShot | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|