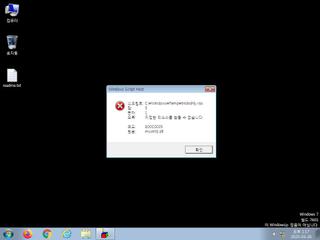
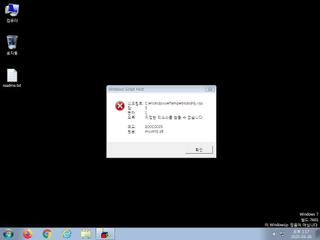
ScreenShot
| Created | 2025.03.26 13:22 | Machine | s1_win7_x6401 |
| Filename | nicworkingskillbetterwithnicetechnology.hta | ||
| Type | HTML document, ASCII text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | 8 detected (Possible, SCRDL, Detected) | ||
| md5 | 6fe3875062cb2b402b33d335dee94ac6 | ||
| sha256 | 320a04fb95efb890a88502f4d81b9efe2d9c953fd85aa4c462164740f412c09c | ||
| ssdeep | 24:hPgWw2dSAT/Pz3oh7ATLuLVpTio+tVBx7xEypwy1ZpgUTMCO:tgNqSme8uBpTio+tPx887gU4CO | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (12cnts)
| Level | Description |
|---|---|
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | The process wscript.exe wrote an executable file to disk |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
| watch | wscript.exe-based dropper (JScript |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | File has been identified by 8 AntiVirus engines on VirusTotal as malicious |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
Rules (31cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Network_Downloader | File Downloader | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
Suricata ids
ET INFO TLS Handshake Failure
ET INFO Pastebin-like Service Domain in DNS Lookup (dpaste .com)
ET INFO Observed Pastebin-like Service Domain (dpaste .com) in TLS SNI
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Pastebin-like Service Domain in DNS Lookup (dpaste .com)
ET INFO Observed Pastebin-like Service Domain (dpaste .com) in TLS SNI
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)