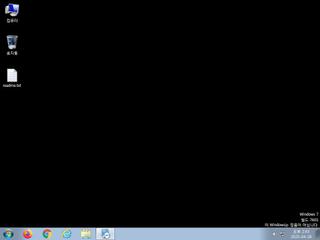
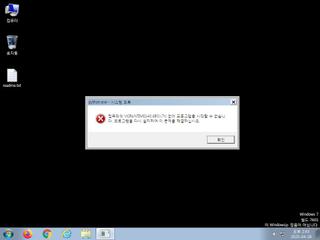
ScreenShot
| Created | 2025.04.28 14:59 | Machine | s1_win7_x6401 |
| Filename | setup.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 33 detected (Dedok, FMHC, Unsafe, malicious, moderate confidence, AveMaria, Detected, Yomal, ABTrojan, SHDG, Artemis, Sefalod, R002H09DI25, Gencirc, susgen, Wacapew, C9nj) | ||
| md5 | eb497402e6fcb1c7cfb3f129bcc4f3f0 | ||
| sha256 | 4e256572e001b76872074878f8ecd2be3f237c9b3a18d0059e2f4a3888579b5b | ||
| ssdeep | 98304:1JcUQLUGrupb8ECxXEvb9ggyld9jz6zrxN26CQQDcbCC+BFlO:XPGZKb8EAEvhggylv36rxo6lCbrO | ||
| imphash | d619eda1a774da262071361b928bb2e4 | ||
| impfuzzy | 48:hylnpVOIDk/6AecfYtTE0c1GT+KQ4zuFbv:hylpVNDk/FecfYtT9c4gv | ||
Network IP location
Signature (20cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 33 AntiVirus engines on VirusTotal as malicious |
| watch | Found URLs in memory pointing to an IP address rather than a domain (potentially indicative of Command & Control traffic) |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates (office) documents on the filesystem |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Steals private information from local Internet browsers |
| notice | Terminates another process |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | One or more processes crashed |
| info | Tries to locate where the browsers are installed |
Rules (60cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Client_SW_User_Data_Stealer | Client_SW_User_Data_Stealer | memory |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| warning | infoStealer_browser_Zero | browser info stealer | memory |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | ASPack_Zero | ASPack packed file | binaries (upload) |
| watch | Chrome_User_Data_Check_Zero | Google Chrome User Data Check | memory |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Network_Downloader | File Downloader | binaries (download) |
| watch | Network_Downloader | File Downloader | binaries (upload) |
| watch | Network_Downloader | File Downloader | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | BitCoin | Perform crypto currency mining | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | PDF_Format_Z | PDF Format | binaries (download) |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | Virtual_currency_Zero | Virtual currency | memory |
| info | vmdetect | Possibly employs anti-virtualization techniques | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x40700c LoadLibraryA
0x407010 lstrcpyA
0x407014 lstrcatA
0x407018 lstrlenA
0x40701c GetSystemDirectoryA
0x407020 GetProcAddress
0x407024 GetModuleHandleA
0x407028 _lclose
0x40702c GetModuleFileNameA
0x407030 _lread
0x407034 _llseek
0x407038 _lopen
0x40703c _lwrite
0x407040 _lcreat
0x407044 CreateDirectoryA
0x407048 SetCurrentDirectoryA
0x40704c GetDiskFreeSpaceA
0x407050 GetFileAttributesA
0x407054 CompareStringA
0x407058 DeleteFileA
0x40705c GetTempPathA
0x407060 GetCurrentDirectoryA
0x407064 CloseHandle
0x407068 GetExitCodeProcess
0x40706c GetLastError
0x407070 LocalFree
0x407074 GetCurrentProcess
0x407078 MoveFileExA
0x40707c GetStringTypeW
0x407080 MultiByteToWideChar
0x407084 LCMapStringW
0x407088 HeapReAlloc
0x40708c RtlUnwind
0x407090 HeapSize
0x407094 Sleep
0x407098 RemoveDirectoryA
0x40709c FreeLibrary
0x4070a0 IsValidCodePage
0x4070a4 GetOEMCP
0x4070a8 GetModuleHandleW
0x4070ac ExitProcess
0x4070b0 DecodePointer
0x4070b4 HeapFree
0x4070b8 HeapAlloc
0x4070bc GetCommandLineA
0x4070c0 HeapSetInformation
0x4070c4 GetStartupInfoW
0x4070c8 InitializeCriticalSectionAndSpinCount
0x4070cc DeleteCriticalSection
0x4070d0 LeaveCriticalSection
0x4070d4 EnterCriticalSection
0x4070d8 EncodePointer
0x4070dc LoadLibraryW
0x4070e0 UnhandledExceptionFilter
0x4070e4 SetUnhandledExceptionFilter
0x4070e8 IsDebuggerPresent
0x4070ec TerminateProcess
0x4070f0 TlsAlloc
0x4070f4 TlsGetValue
0x4070f8 TlsSetValue
0x4070fc TlsFree
0x407100 InterlockedIncrement
0x407104 SetLastError
0x407108 GetCurrentThreadId
0x40710c InterlockedDecrement
0x407110 WriteFile
0x407114 GetStdHandle
0x407118 GetModuleFileNameW
0x40711c IsProcessorFeaturePresent
0x407120 HeapCreate
0x407124 FreeEnvironmentStringsW
0x407128 WideCharToMultiByte
0x40712c GetEnvironmentStringsW
0x407130 SetHandleCount
0x407134 GetFileType
0x407138 QueryPerformanceCounter
0x40713c GetTickCount
0x407140 GetCurrentProcessId
0x407144 GetSystemTimeAsFileTime
0x407148 GetCPInfo
0x40714c GetACP
USER32.dll
0x40715c TranslateMessage
0x407160 DispatchMessageA
0x407164 PeekMessageA
0x407168 wsprintfA
0x40716c LoadCursorA
0x407170 SetCursor
0x407174 MessageBoxA
0x407178 MsgWaitForMultipleObjects
ADVAPI32.dll
0x407000 GetTokenInformation
0x407004 OpenProcessToken
SHELL32.dll
0x407154 ShellExecuteExA
EAT(Export Address Table) is none
KERNEL32.dll
0x40700c LoadLibraryA
0x407010 lstrcpyA
0x407014 lstrcatA
0x407018 lstrlenA
0x40701c GetSystemDirectoryA
0x407020 GetProcAddress
0x407024 GetModuleHandleA
0x407028 _lclose
0x40702c GetModuleFileNameA
0x407030 _lread
0x407034 _llseek
0x407038 _lopen
0x40703c _lwrite
0x407040 _lcreat
0x407044 CreateDirectoryA
0x407048 SetCurrentDirectoryA
0x40704c GetDiskFreeSpaceA
0x407050 GetFileAttributesA
0x407054 CompareStringA
0x407058 DeleteFileA
0x40705c GetTempPathA
0x407060 GetCurrentDirectoryA
0x407064 CloseHandle
0x407068 GetExitCodeProcess
0x40706c GetLastError
0x407070 LocalFree
0x407074 GetCurrentProcess
0x407078 MoveFileExA
0x40707c GetStringTypeW
0x407080 MultiByteToWideChar
0x407084 LCMapStringW
0x407088 HeapReAlloc
0x40708c RtlUnwind
0x407090 HeapSize
0x407094 Sleep
0x407098 RemoveDirectoryA
0x40709c FreeLibrary
0x4070a0 IsValidCodePage
0x4070a4 GetOEMCP
0x4070a8 GetModuleHandleW
0x4070ac ExitProcess
0x4070b0 DecodePointer
0x4070b4 HeapFree
0x4070b8 HeapAlloc
0x4070bc GetCommandLineA
0x4070c0 HeapSetInformation
0x4070c4 GetStartupInfoW
0x4070c8 InitializeCriticalSectionAndSpinCount
0x4070cc DeleteCriticalSection
0x4070d0 LeaveCriticalSection
0x4070d4 EnterCriticalSection
0x4070d8 EncodePointer
0x4070dc LoadLibraryW
0x4070e0 UnhandledExceptionFilter
0x4070e4 SetUnhandledExceptionFilter
0x4070e8 IsDebuggerPresent
0x4070ec TerminateProcess
0x4070f0 TlsAlloc
0x4070f4 TlsGetValue
0x4070f8 TlsSetValue
0x4070fc TlsFree
0x407100 InterlockedIncrement
0x407104 SetLastError
0x407108 GetCurrentThreadId
0x40710c InterlockedDecrement
0x407110 WriteFile
0x407114 GetStdHandle
0x407118 GetModuleFileNameW
0x40711c IsProcessorFeaturePresent
0x407120 HeapCreate
0x407124 FreeEnvironmentStringsW
0x407128 WideCharToMultiByte
0x40712c GetEnvironmentStringsW
0x407130 SetHandleCount
0x407134 GetFileType
0x407138 QueryPerformanceCounter
0x40713c GetTickCount
0x407140 GetCurrentProcessId
0x407144 GetSystemTimeAsFileTime
0x407148 GetCPInfo
0x40714c GetACP
USER32.dll
0x40715c TranslateMessage
0x407160 DispatchMessageA
0x407164 PeekMessageA
0x407168 wsprintfA
0x40716c LoadCursorA
0x407170 SetCursor
0x407174 MessageBoxA
0x407178 MsgWaitForMultipleObjects
ADVAPI32.dll
0x407000 GetTokenInformation
0x407004 OpenProcessToken
SHELL32.dll
0x407154 ShellExecuteExA
EAT(Export Address Table) is none