ScreenShot
| Created | 2025.04.21 13:37 | Machine | s1_win7_x6401 |
| Filename | random.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | abba1541f190e3c8e0afe7d473f14a25 | ||
| sha256 | d6d5e5483da9d26a14715bf8cf5aa4a1a5a50a2075bb3a09715ee27585bd97fc | ||
| ssdeep | 98304:njXNPv+KZKlxgmAluFBOisqBgmlnxImZpmPiGdQ+QAvTorwt:jdPh6xL2uF8NqJdq5Q+nvkE | ||
| imphash | 2eabe9054cad5152567f0699947a2c5b | ||
| impfuzzy | 3:sBv:A | ||
Network IP location
Signature (12cnts)
| Level | Description |
|---|---|
| watch | Checks for the presence of known devices from debuggers and forensic tools |
| watch | Checks for the presence of known windows from debuggers and forensic tools |
| watch | Checks the version of Bios |
| watch | Detects VMWare through the in instruction feature |
| notice | A process attempted to delay the analysis task. |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Expresses interest in specific running processes |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks if process is being debugged by a debugger |
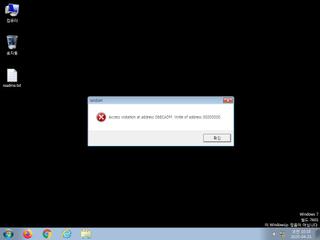
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | themida_packer | themida packer | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
kernel32.dll
0x90303e lstrcpy
EAT(Export Address Table) is none
kernel32.dll
0x90303e lstrcpy
EAT(Export Address Table) is none