ScreenShot
| Created | 2024.10.06 18:28 | Machine | s1_win7_x6403 |
| Filename | licarisan_api.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 44 detected (AIDetectMalware, Loader, Malicious, score, ObfuscatedPoly, Artemis, Unsafe, Midie, Attribute, HighConfidence, moderate confidence, GenKryptik, HCAH, RATX, ccmw, CLASSIC, Kryptik, yyfda, Remcos, Detected, Wacatac, R670029, Outbreak, R014H09J524, Sgil) | ||
| md5 | 65a683124fc4ca1839e95322370e2b0d | ||
| sha256 | 3ff0d50557b5ba7eb306048c0e20dd4304a75aeab0470fe213c5089a031a396f | ||
| ssdeep | 49152:bP70hwGvLJT/a9yLe7lAsYaxBjbdOGMneGzxgUgoJUcaqCDx6ITcP2MNoSPhaC+O:nUgoJUBZJoP2MNBajvXOSq | ||
| imphash | 33e003ddaff3bc71480e8cb946f52917 | ||
| impfuzzy | 48:ouIJi16NolHzi63l1dTddlBl/x5gWr/nBWcoa1+:tlHzv3lXRdlrP9E | ||
Network IP location
Signature (34cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| danger | File has been identified by 44 AntiVirus engines on VirusTotal as malicious |
| danger | Executed a process and injected code into it |
| watch | Allocates execute permission to another process indicative of possible code injection |
| watch | Code injection by writing an executable or DLL to the memory of another process |
| watch | Communicates with host for which no DNS query was performed |
| watch | Created a process named as a common system process |
| watch | Creates a suspicious Powershell process |
| watch | Installs itself for autorun at Windows startup |
| watch | One or more of the buffers contains an embedded PE file |
| watch | Potential code injection by writing to the memory of another process |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Used NtSetContextThread to modify a thread in a remote process indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Foreign language identified in PE resource |
| notice | One or more potentially interesting buffers were extracted |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
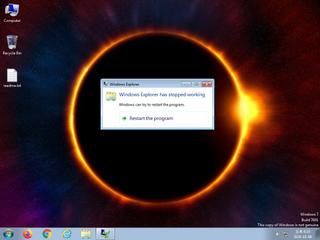
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | The executable uses a known packer |
| info | The file contains an unknown PE resource name possibly indicative of a packer |
| info | Tries to locate where the browsers are installed |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (50cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (upload) |
| watch | Network_Downloader | File Downloader | memory |
| watch | schtasks_Zero | task schedule | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_antivirus | Disable AntiVirus | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PowerShell | PowerShell script | scripts |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
PE API
IAT(Import Address Table) Library
gdi32.dll
0x4f2338 TextOutW
0x4f233c StretchDIBits
0x4f2340 StretchBlt
0x4f2344 SetWindowOrgEx
0x4f2348 SetViewportOrgEx
0x4f234c SetTextColor
0x4f2350 SetStretchBltMode
0x4f2354 SetROP2
0x4f2358 SetPixelV
0x4f235c SetPixel
0x4f2360 SetDIBitsToDevice
0x4f2364 SetDIBits
0x4f2368 SetBkMode
0x4f236c SetBkColor
0x4f2370 SelectPalette
0x4f2374 SelectObject
0x4f2378 SelectClipRgn
0x4f237c SaveDC
0x4f2380 RoundRect
0x4f2384 RestoreDC
0x4f2388 ResizePalette
0x4f238c Rectangle
0x4f2390 RectVisible
0x4f2394 RealizePalette
0x4f2398 Polyline
0x4f239c OffsetViewportOrgEx
0x4f23a0 MoveToEx
0x4f23a4 LineTo
0x4f23a8 IntersectClipRect
0x4f23ac GetViewportOrgEx
0x4f23b0 GetTextMetricsW
0x4f23b4 GetTextExtentPoint32W
0x4f23b8 GetTextExtentExPointW
0x4f23bc GetTextColor
0x4f23c0 GetTextAlign
0x4f23c4 GetStockObject
0x4f23c8 GetROP2
0x4f23cc GetPixel
0x4f23d0 GetPaletteEntries
0x4f23d4 GetObjectType
0x4f23d8 GetObjectW
0x4f23dc GetNearestPaletteIndex
0x4f23e0 GetDeviceCaps
0x4f23e4 GetDIBits
0x4f23e8 GetCurrentPositionEx
0x4f23ec GetCurrentObject
0x4f23f0 GetClipBox
0x4f23f4 GetBkMode
0x4f23f8 GetBkColor
0x4f23fc ExtTextOutW
0x4f2400 ExcludeClipRect
0x4f2404 Ellipse
0x4f2408 DeleteObject
0x4f240c DeleteDC
0x4f2410 CreateRoundRectRgn
0x4f2414 CreateRectRgn
0x4f2418 CreatePolygonRgn
0x4f241c CreatePenIndirect
0x4f2420 CreatePen
0x4f2424 CreatePalette
0x4f2428 CreateHalftonePalette
0x4f242c CreateFontIndirectW
0x4f2430 CreateDIBSection
0x4f2434 CreateCompatibleDC
0x4f2438 CreateCompatibleBitmap
0x4f243c CreateBrushIndirect
0x4f2440 CombineRgn
0x4f2444 BitBlt
kernel32.dll
0x4f244c lstrcmpW
0x4f2450 WriteProcessMemory
0x4f2454 WritePrivateProfileStringW
0x4f2458 WriteFile
0x4f245c WaitForSingleObject
0x4f2460 VirtualQuery
0x4f2464 VirtualProtect
0x4f2468 UnmapViewOfFile
0x4f246c TerminateProcess
0x4f2470 SystemTimeToFileTime
0x4f2474 Sleep
0x4f2478 ReadProcessMemory
0x4f247c QueryDosDeviceW
0x4f2480 OutputDebugStringW
0x4f2484 OpenProcess
0x4f2488 MulDiv
0x4f248c MapViewOfFile
0x4f2490 LocalFree
0x4f2494 LocalAlloc
0x4f2498 LoadLibraryW
0x4f249c LeaveCriticalSection
0x4f24a0 IsBadCodePtr
0x4f24a4 InitializeCriticalSection
0x4f24a8 HeapFree
0x4f24ac HeapDestroy
0x4f24b0 HeapAlloc
0x4f24b4 GlobalUnlock
0x4f24b8 GlobalMemoryStatus
0x4f24bc GlobalHandle
0x4f24c0 GlobalLock
0x4f24c4 GlobalGetAtomNameW
0x4f24c8 GlobalFree
0x4f24cc GlobalDeleteAtom
0x4f24d0 GlobalAlloc
0x4f24d4 GlobalAddAtomW
0x4f24d8 GetWindowsDirectoryW
0x4f24dc GetVersionExW
0x4f24e0 GetVersion
0x4f24e4 GetTickCount
0x4f24e8 GetTempPathW
0x4f24ec GetSystemTime
0x4f24f0 GetSystemInfo
0x4f24f4 GetSystemDirectoryW
0x4f24f8 GetProcessTimes
0x4f24fc GetProcAddress
0x4f2500 GetPrivateProfileStringW
0x4f2504 GetPriorityClass
0x4f2508 GetModuleHandleW
0x4f250c GetModuleFileNameW
0x4f2510 GetLogicalDriveStringsW
0x4f2514 GetLastError
0x4f2518 GetDriveTypeW
0x4f251c GetDiskFreeSpaceExW
0x4f2520 GetCurrentThreadId
0x4f2524 GetCurrentProcess
0x4f2528 InterlockedIncrement
0x4f252c InterlockedExchangeAdd
0x4f2530 InterlockedExchange
0x4f2534 InterlockedDecrement
0x4f2538 InterlockedCompareExchange
0x4f253c FreeLibrary
0x4f2540 FlushInstructionCache
0x4f2544 FileTimeToSystemTime
0x4f2548 EnterCriticalSection
0x4f254c CreateMutexW
0x4f2550 CreateFileMappingW
0x4f2554 CreateFileW
0x4f2558 CopyFileW
0x4f255c CloseHandle
advapi32.dll
0x4f2564 RegQueryValueExW
0x4f2568 RegOpenKeyExW
0x4f256c RegFlushKey
0x4f2570 RegCloseKey
0x4f2574 OpenProcessToken
0x4f2578 LookupPrivilegeValueW
0x4f257c GetUserNameW
0x4f2580 AdjustTokenPrivileges
shell32.dll
0x4f263c SHGetFileInfoW
0x4f2640 ExtractIconW
shell32.dll
0x4f2648 SHGetSpecialFolderPathW
0x4f264c SHGetPathFromIDListW
0x4f2650 SHBrowseForFolderW
ole32.dll
0x4f2658 CoCreateInstance
comctl32.dll
0x4f2660 _TrackMouseEvent
0x4f2664 ImageList_GetIconSize
0x4f2668 ImageList_Draw
Kernel32.dll
0x4f2670 GetLongPathNameW
kernel32.dll
0x4f2df4 Sleep
ole32.dll
0x4f2dfc IsEqualGUID
comctl32.dll
0x4f38dc ImageList_GetIconSize
user32.dll
0x4f3950 PrivateExtractIconsW
kernel32.dll
0x4f3958 VerSetConditionMask
0x4f395c VerifyVersionInfoW
EAT(Export Address Table) is none
gdi32.dll
0x4f2338 TextOutW
0x4f233c StretchDIBits
0x4f2340 StretchBlt
0x4f2344 SetWindowOrgEx
0x4f2348 SetViewportOrgEx
0x4f234c SetTextColor
0x4f2350 SetStretchBltMode
0x4f2354 SetROP2
0x4f2358 SetPixelV
0x4f235c SetPixel
0x4f2360 SetDIBitsToDevice
0x4f2364 SetDIBits
0x4f2368 SetBkMode
0x4f236c SetBkColor
0x4f2370 SelectPalette
0x4f2374 SelectObject
0x4f2378 SelectClipRgn
0x4f237c SaveDC
0x4f2380 RoundRect
0x4f2384 RestoreDC
0x4f2388 ResizePalette
0x4f238c Rectangle
0x4f2390 RectVisible
0x4f2394 RealizePalette
0x4f2398 Polyline
0x4f239c OffsetViewportOrgEx
0x4f23a0 MoveToEx
0x4f23a4 LineTo
0x4f23a8 IntersectClipRect
0x4f23ac GetViewportOrgEx
0x4f23b0 GetTextMetricsW
0x4f23b4 GetTextExtentPoint32W
0x4f23b8 GetTextExtentExPointW
0x4f23bc GetTextColor
0x4f23c0 GetTextAlign
0x4f23c4 GetStockObject
0x4f23c8 GetROP2
0x4f23cc GetPixel
0x4f23d0 GetPaletteEntries
0x4f23d4 GetObjectType
0x4f23d8 GetObjectW
0x4f23dc GetNearestPaletteIndex
0x4f23e0 GetDeviceCaps
0x4f23e4 GetDIBits
0x4f23e8 GetCurrentPositionEx
0x4f23ec GetCurrentObject
0x4f23f0 GetClipBox
0x4f23f4 GetBkMode
0x4f23f8 GetBkColor
0x4f23fc ExtTextOutW
0x4f2400 ExcludeClipRect
0x4f2404 Ellipse
0x4f2408 DeleteObject
0x4f240c DeleteDC
0x4f2410 CreateRoundRectRgn
0x4f2414 CreateRectRgn
0x4f2418 CreatePolygonRgn
0x4f241c CreatePenIndirect
0x4f2420 CreatePen
0x4f2424 CreatePalette
0x4f2428 CreateHalftonePalette
0x4f242c CreateFontIndirectW
0x4f2430 CreateDIBSection
0x4f2434 CreateCompatibleDC
0x4f2438 CreateCompatibleBitmap
0x4f243c CreateBrushIndirect
0x4f2440 CombineRgn
0x4f2444 BitBlt
kernel32.dll
0x4f244c lstrcmpW
0x4f2450 WriteProcessMemory
0x4f2454 WritePrivateProfileStringW
0x4f2458 WriteFile
0x4f245c WaitForSingleObject
0x4f2460 VirtualQuery
0x4f2464 VirtualProtect
0x4f2468 UnmapViewOfFile
0x4f246c TerminateProcess
0x4f2470 SystemTimeToFileTime
0x4f2474 Sleep
0x4f2478 ReadProcessMemory
0x4f247c QueryDosDeviceW
0x4f2480 OutputDebugStringW
0x4f2484 OpenProcess
0x4f2488 MulDiv
0x4f248c MapViewOfFile
0x4f2490 LocalFree
0x4f2494 LocalAlloc
0x4f2498 LoadLibraryW
0x4f249c LeaveCriticalSection
0x4f24a0 IsBadCodePtr
0x4f24a4 InitializeCriticalSection
0x4f24a8 HeapFree
0x4f24ac HeapDestroy
0x4f24b0 HeapAlloc
0x4f24b4 GlobalUnlock
0x4f24b8 GlobalMemoryStatus
0x4f24bc GlobalHandle
0x4f24c0 GlobalLock
0x4f24c4 GlobalGetAtomNameW
0x4f24c8 GlobalFree
0x4f24cc GlobalDeleteAtom
0x4f24d0 GlobalAlloc
0x4f24d4 GlobalAddAtomW
0x4f24d8 GetWindowsDirectoryW
0x4f24dc GetVersionExW
0x4f24e0 GetVersion
0x4f24e4 GetTickCount
0x4f24e8 GetTempPathW
0x4f24ec GetSystemTime
0x4f24f0 GetSystemInfo
0x4f24f4 GetSystemDirectoryW
0x4f24f8 GetProcessTimes
0x4f24fc GetProcAddress
0x4f2500 GetPrivateProfileStringW
0x4f2504 GetPriorityClass
0x4f2508 GetModuleHandleW
0x4f250c GetModuleFileNameW
0x4f2510 GetLogicalDriveStringsW
0x4f2514 GetLastError
0x4f2518 GetDriveTypeW
0x4f251c GetDiskFreeSpaceExW
0x4f2520 GetCurrentThreadId
0x4f2524 GetCurrentProcess
0x4f2528 InterlockedIncrement
0x4f252c InterlockedExchangeAdd
0x4f2530 InterlockedExchange
0x4f2534 InterlockedDecrement
0x4f2538 InterlockedCompareExchange
0x4f253c FreeLibrary
0x4f2540 FlushInstructionCache
0x4f2544 FileTimeToSystemTime
0x4f2548 EnterCriticalSection
0x4f254c CreateMutexW
0x4f2550 CreateFileMappingW
0x4f2554 CreateFileW
0x4f2558 CopyFileW
0x4f255c CloseHandle
advapi32.dll
0x4f2564 RegQueryValueExW
0x4f2568 RegOpenKeyExW
0x4f256c RegFlushKey
0x4f2570 RegCloseKey
0x4f2574 OpenProcessToken
0x4f2578 LookupPrivilegeValueW
0x4f257c GetUserNameW
0x4f2580 AdjustTokenPrivileges
shell32.dll
0x4f263c SHGetFileInfoW
0x4f2640 ExtractIconW
shell32.dll
0x4f2648 SHGetSpecialFolderPathW
0x4f264c SHGetPathFromIDListW
0x4f2650 SHBrowseForFolderW
ole32.dll
0x4f2658 CoCreateInstance
comctl32.dll
0x4f2660 _TrackMouseEvent
0x4f2664 ImageList_GetIconSize
0x4f2668 ImageList_Draw
Kernel32.dll
0x4f2670 GetLongPathNameW
kernel32.dll
0x4f2df4 Sleep
ole32.dll
0x4f2dfc IsEqualGUID
comctl32.dll
0x4f38dc ImageList_GetIconSize
user32.dll
0x4f3950 PrivateExtractIconsW
kernel32.dll
0x4f3958 VerSetConditionMask
0x4f395c VerifyVersionInfoW
EAT(Export Address Table) is none