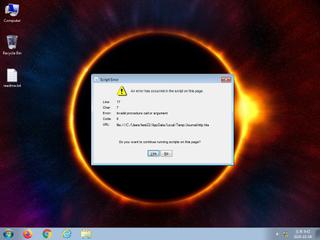
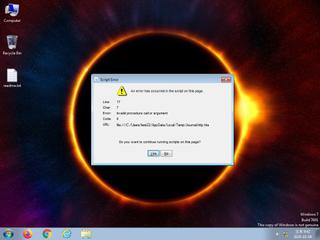
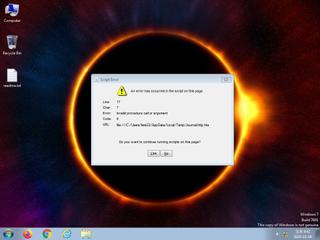
ScreenShot
| Created | 2024.10.08 21:59 | Machine | s1_win7_x6403 |
| Filename | Journal-http.hta | ||
| Type | HTML document, ASCII text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 41 detected (Malicious, score, expkit, CVE-2018-8174, Vrqb, SNIC, COBEACON, TrjGen, ebogzi, CLASSIC, Gen2, Siggen, Inor, Detected, Infected, AutoInfector, NBY@7nkapq, CobaltStrike, Hajl, SXH2XJC) | ||
| md5 | 439ba39a07845e334c3c4422a96bc72b | ||
| sha256 | 836c97307357a8f7a318cf0206b6f1aff82cc71c80fd37ebbfd0777a2dff483a | ||
| ssdeep | 384:kdeiNYnl3Q/2irLwQbyACD1JaSisfUD2O3Al3l0YKxAV6/a:kE3Q/T/weydi4s2O3Al3lqxRS | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 41 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates executable files on the filesystem |
| info | Checks amount of memory in system |
Rules (1cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | PE_Header_Zero | PE File Signature | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|